Blog
Not sure where to start? Let us guide you to the Right Solution
-
Why SMBs Should Securely Migrate to Azure
- June 23, 2025
- Posted by: admin
- Category: Uncategorized
No Comments
On-premises IT may be putting your security at risk. 💼 Ready for a more resilient solution?
This infographic breaks down 💡 how migrating to @Microsoft Azure strengthens your security while paving the way for growth. Discover why Azure is the smarter, safer choice!
-
What is an AI PC? Understanding HP’s Next Generation AI Laptops
- June 23, 2025
- Posted by: admin
- Category: Uncategorized
What exactly is an AI PC? 🤔
They are tools designed to boost productivity and support the way you work best.
Read this blog to see what makes @HP #AI laptops different and how they can help streamline your workflows, boost efficiency, and empower your team. #HPAIPC #FutureOfWork -
Using Copilot in Customer Service
- June 23, 2025
- Posted by: admin
- Category: Uncategorized

Customer service moves fast — every second counts. ⏳
With @Microsoft Copilot, your team can streamline workflows, find answers faster, and enhance every customer interaction. No more information overload or wasted time.
💡 Download the infographic to see how real-time AI support helps you work smarter and resolve issues more efficiently. 👇
-
Email disclaimers: A comprehensive guide to maintaining legal compliance
- June 23, 2025
- Posted by: admin
- Category: Uncategorized
Legal missteps can start with a signature. ⚠️ Check out the blog to learn how to strengthen legal protections with every #email you send. @Exclaimer #emailsignatures #emailsecurity
-
Get business done together, from anywhere
- June 19, 2025
- Posted by: admin
- Category: Uncategorized

DM us if you’d like to discuss digital technology strategies for your SMB with an @Microsoft Office expert from Happens Here Partners.
-
Track and organize your work effortlessly
- June 19, 2025
- Posted by: admin
- Category: Uncategorized
Staying organized is imperative for keeping your business on track. Comment if you’d like to discuss strategies for your SMB with an @Microsoft Office expert from Happens Here Partners.
-
Security Program Considerations
- June 18, 2025
- Posted by: admin
- Category: Uncategorized
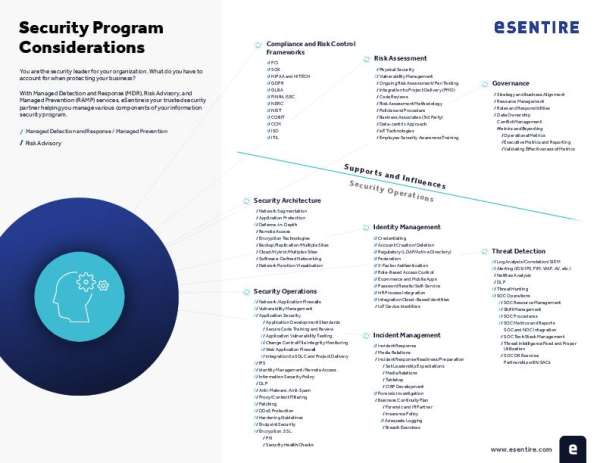
Security program gaps can’t be ignored. ⚠️ Download this eBook for help identifying and closing them.
Then, follow up by messaging us to discuss how @eSentire and Happens Here Partners can support your organization’s security strategy.
-
How to Use Microsoft Copilot in Communications
- June 18, 2025
- Posted by: admin
- Category: Uncategorized

Are you getting the most out of Microsoft Copilot for communications? 🤔
This concise, 7-minute video demo highlights how Copilot can streamline content creation, fine-tune messaging, and automate daily workflows — all tailored for communications professionals.
🎥 Watch one of the most practical and informative Copilot walkthroughs available.
-
Enhance ABM with Exclaimer’s CRM Email Integrations
- June 18, 2025
- Posted by: admin
- Category: Uncategorized
A successful ABM strategy depends on consistency, personalization, and precision.
💡 That’s where Exclaimer’s CRM integrations come in. By connecting to platforms like Salesforce or HubSpot, Exclaimer ensures every email signature aligns with your campaigns, contact segments, and brand guidelines.
Read the blog from @Exclaimer for a breakdown of how these integrations streamline execution, improve targeting, and support cohesive communications.
-
Combat cyberthreats as a unified force
- June 18, 2025
- Posted by: admin
- Category: Uncategorized
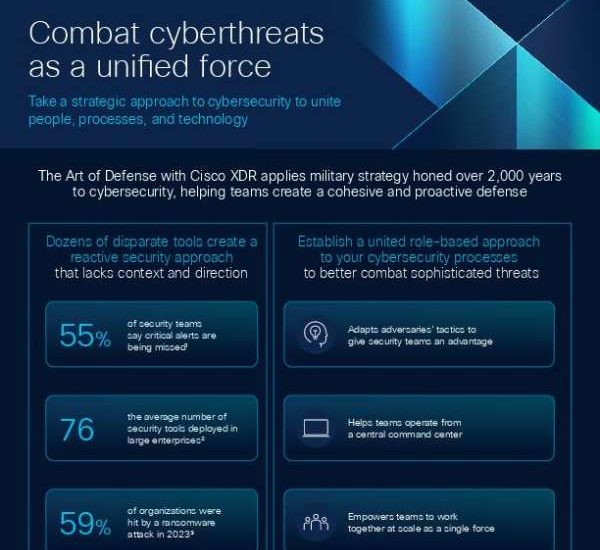
Explore how Cisco’s XDR Automation solution reshapes cybersecurity – turning disparate tools into a unified force. Diving into this week’s content! Cybersecurity reimagined with #Cisco XDR Automation. Proactive defense, automated tools, cohesive teams – the future of cybersecurity is here. Check out our infographic and contact Happens Here Partners to get started with the new XDR today.
